Creating a Google Cloud Services Connection for an MVE with Cisco SD-WAN
You can create a network connection from an MVE (a Cisco interconnect gateway) to Google Cloud through Partner Interconnect.
When connecting to Google Cloud Platform (GCP) through Partner Interconnect with Megaport, the Virtual Cross Connect (VXC) forms the Layer 2 component of the connection and Layer 3 BGP is established directly between the customer and GCP.
Important
Before you begin, create an MVE (Cisco interconnect gateway) in vManage. For more information, see Creating an MVE. The MVE needs to be in the active state.
There are three parts to adding a Google Cloud connection to your MVE and vManage.
-
Create a Partner Interconnect attachment in Google Cloud Console or gcloud CLI. Copy the pairing key that is provided as part of the attachment creation.
For more information, see the Google documentation on Google Partner Interconnects. -
In the Megaport Portal, create a VXC from your MVE to connect to your Google Cloud attachment.
-
In vManage, create a custom MVE device template and add the details of the Google Cloud connection.
These instructions step through the second and third parts.
Note
The initial release of MVE requires configuration steps in both Cisco vManage and the Megaport Portal for Google cloud connections (as described in this topic). Subsequent updates by Cisco let you configure Google connections completely in vManage. When possible, we recommend creating Google connections in vManage for seamless integration with your Cisco SD-WAN environment. Cisco provides instructions for the vManage steps: Create Interconnects to Google Cloud.
Adding the Google Cloud connection in the Megaport Portal
To set up the GCP connection, you need to create the connection in the Megaport Portal.
To deploy a VXC to Google Cloud Platform from the Megaport Portal
-
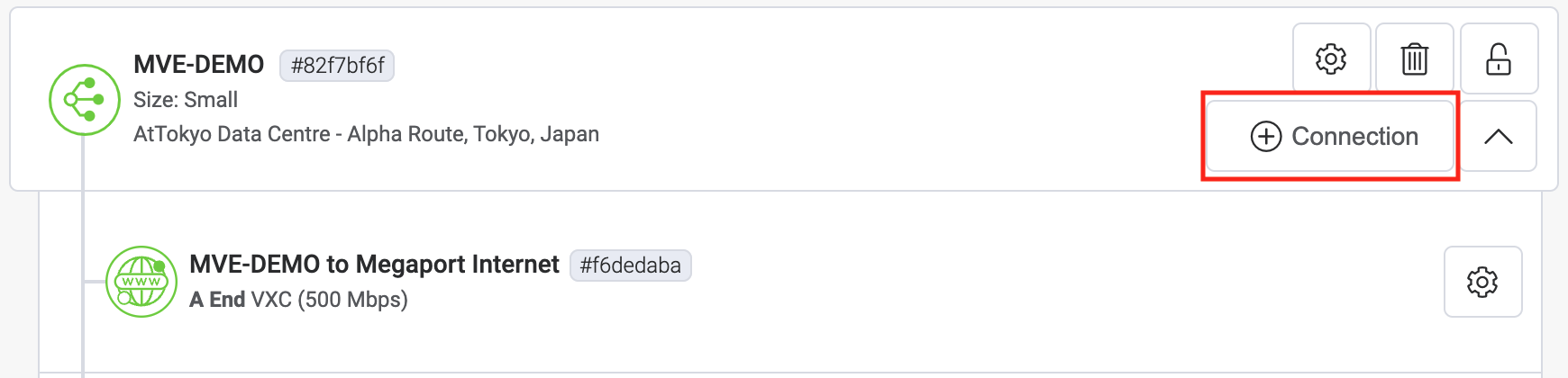
In the Megaport Portal, go to the Services page and select the MVE for the connection.
-
Click +Connection then click Cloud.
-
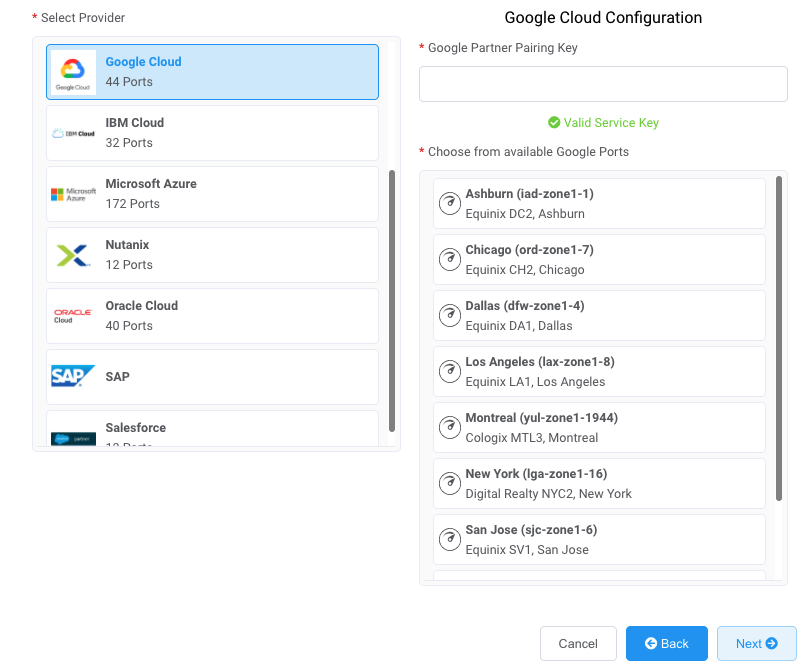
Select Google as the provider.
Tip
To check the latency and price of connecting to a particular Google location, click View all Google Partner locations. You can proceed to the Connection Details page without a pairing key and review the pricing of the selected port. To place an order for a Google connection, you need to provide a pairing key.
-
Copy and paste the pairing key from the Google Cloud console into the Google Partner Pairing Key field.
The relevant Google targets appear based on the region of your GCI Partner connection. -
Select the target location for your connection then click Next.
-
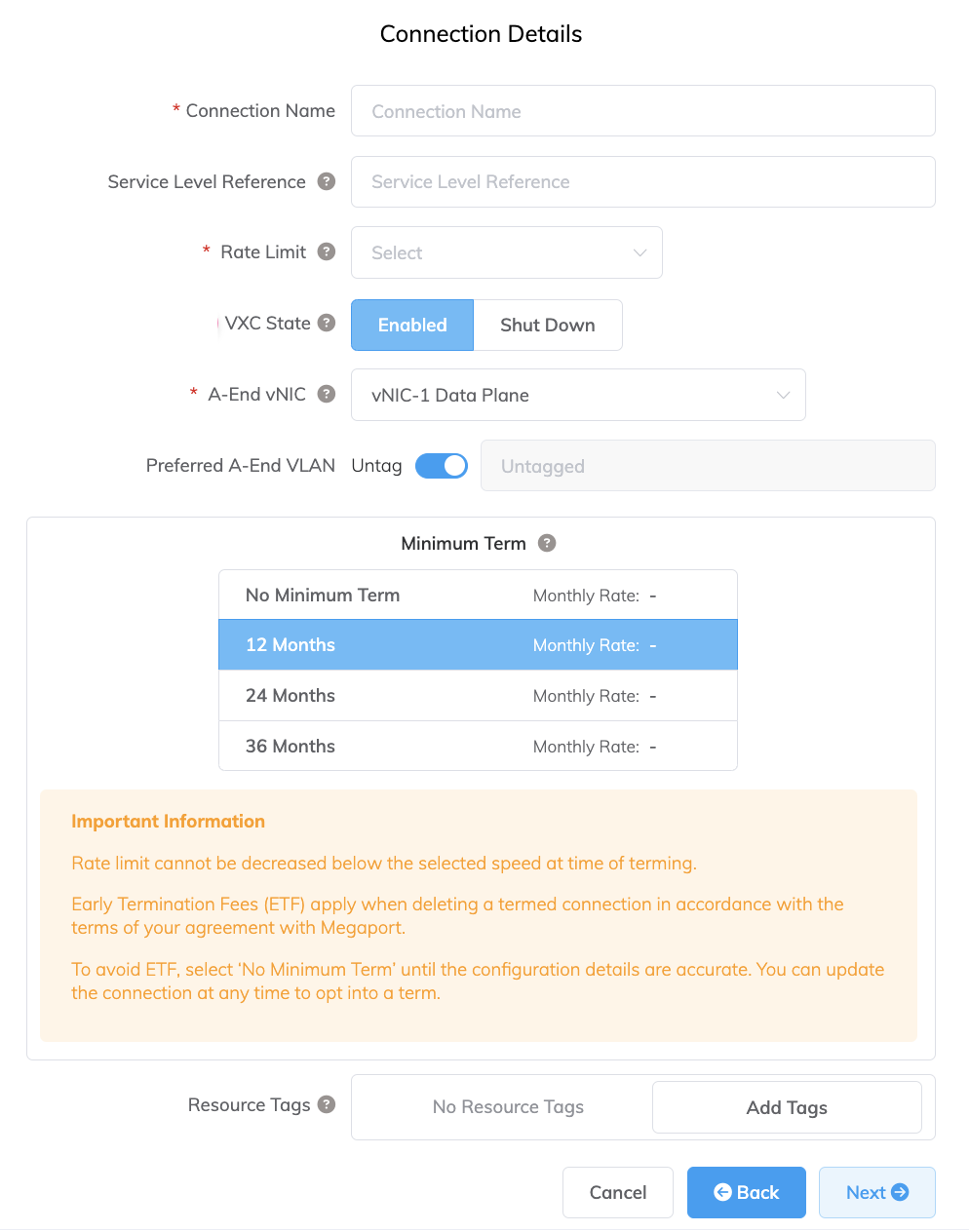
Specify the connection details:
-
Connection Name – The name of your VXC to be shown in the Megaport Portal.
-
Service Level Reference (optional) – Specify a unique identifying number for your Megaport service to be used for billing purposes, such as a cost center number, unique customer ID, or purchase order number. The service level reference number appears for each service under the Product section of the invoice. You can also edit this field for an existing service.
-
Rate Limit – The speed of your connection in Mbps. Enter the same rate you selected for your Google port speed.
-
VXC State – Select Enabled or Shut Down to define the initial state of the connection. For more information, see Shutting Down a VXC for Failover Testing.
Note
If you select Shut Down, traffic will not flow through this service and it will behave as if it was down on the Megaport network. Billing for this service will remain active and you will still be charged for this connection.
-
A-End vNIC – Select an A-End vNIC from the drop-down list. For more information about vNICs, see Creating an MVE in the Megaport Portal.
-
Preferred A-End VLAN – The VLAN for this connection that you will receive through the MVE. This must be a unique VLAN ID on this MVE and can range from 2 to 4093. If you specify a VLAN ID that is already in use, the system displays the next available VLAN number. The VLAN ID must be unique to proceed with the order. If you don’t specify a value, Megaport will assign one.
-
Minimum Term – Select No Minimum Term, 12 Months, 24 Months, 36 Months, 48 Months, or 60 Months. Longer terms result in a lower monthly rate. 12 Months is selected by default. Take note of the information on the screen to avoid early termination fees (ETF).
Enable the Minimum Term Renewal option for services with a 12, 24, 36, 48 or 60-month term to automatically renew the contract at the same discounted price and term length at the end of the contract. If you don’t renew the contract, at the end of the term, the contract will automatically roll over to month-to-month contract for the following billing period, at the same price, without term discounts.
For more information, see VXC Pricing and Contract Terms and VXC, Megaport Internet, and IX Billing.
-
Resource Tags – You can use resource tags to add your own reference metadata to a Megaport service.
To add a tag:- Click Add Tags.
- Click Add New Tag.
- Enter details into the fields:
- Key – string maximum length 128. Valid values are a-z 0-9 _ : . / \ -
- Value – string maximum length 256. Valid values are a-z A-Z 0-9 _ : . @ / + \ - (space)
- Click Save.
If you already have resource tags for that service, you can manage them by clicking Manage Tags.
Warning
Never include sensitive information in a resource tag. Sensitive information includes commands that return existing tag definitions and information that will identify a person or company.
-
-
Add the VXC to your order and complete the checkout process.
-
Once you have deployed the VXC, go back to your attachment in the Google Cloud Console and accept the attachment. You will be provided your private IP address from Google to configure BGP.
Ensure that you pre-activate the attachment or mark the attachment as active after configuring the VXC. Otherwise, you cannot set up BGP with your SD-WAN instance.
Note
The Google ASN will always be 16550.
Adding the Google Cloud connection to vManage
Follow the steps in each of these sections to create, edit, and attach the vManage templates for an MVE with the connection details.
To set up the connection in vManage, you need a dedicated device template and you need to provide feature templates to specify configuration details. You need to create a Service VPN template, a Cisco BGP template, as well as a CLI add-on template.
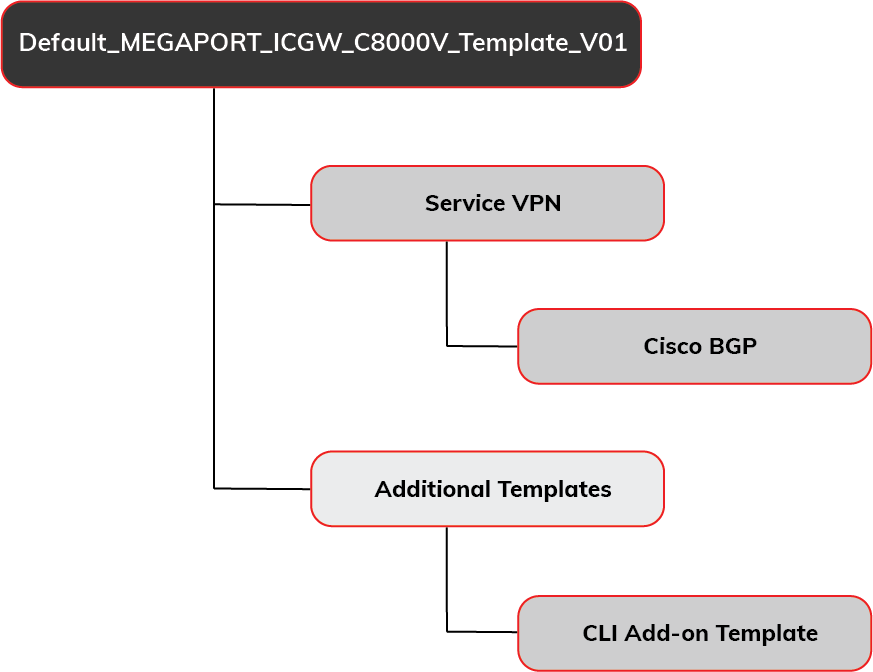
Step 1 - Copy the default device template
You need a dedicated template for the MVE so you can edit the template with the connection details for the VXC. You need a dedicated template because if other devices are attached to the template, the change affects each attached device.
To create a copy of the device template
-
In vManage, go to Configure > Templates and select the Device tab.
-
Find the Default_MEGAPORT_ICGW_C8000V_Template_V01 template and copy it.
Click the ellipsis (…) at the end of the row and choose Copy from the drop-down menu. -
Enter a name for the template and a description and click Copy.
This name can contain only uppercase and lowercase letters, the digits 0 through 9, hyphens, and underscores. It cannot contain spaces or any other characters.
Step 2 - Create a Cisco VPN feature template
You need to create a VPN template so you can specify the VPN ID of the GCP connection. The VPN ID is the same as the corporate network.
To create a VPN feature template
-
In vManage, go to Configure > Templates and select the Feature tab.
-
Find a template for the C8000v device model and a type of Cisco VPN and copy it.
Click the ellipsis (…) at the end of the row and choose Copy from the drop-down menu.Note
Instead of copying the template, you can also add a new Cisco VPN template for a C8000v device and populate it with the same values.
-
Enter a name for the template and a description and click Copy.
-
Edit the template and add the VPN ID in the Basic Configuration.
Click the ellipsis (…) and choose Edit.
The VPN ID can be any number 1 – 511 or 513 – 65530. VPN 0 is reserved for Transport VPN and VPN 512 is reserved for Managed VPN. The number is normally identical to the VPN ID assigned for corporate networks to communicate between the corporate network and cloud service. -
Click Update.
Step 3 - Create a BGP feature template
You also need a BGP template for the connection peering details.
To create a Cisco BGP feature template
-
In the Feature tab of vManage Templates, find a template for the C8000v device model and a type of Cisco BGP and copy it.
Note
Instead of copying the template, you can also add a new Cisco BGP template for a C8000v device and populate it with the same values.
-
Enter a name for the template and a description and click Copy.
-
Edit the template (click the ellipsis … for the new template and choose Edit) and enter the AS Number for the MVE in the Basic Configuration section.
-
In the Neighbor section, click +New Neighbor and specify these values for the cloud side of the connection:
- Address – Specify the peer IP address of the cloud side. Enter the IP address and subnet mask in dotted quad format and not CIDR notation. For example, specify
169.254.x.y 255.255.255.248instead ofa.b.c.d/29. - Description – Enter a meaningful description of the template.
- Remote AS – Enter the AS Number of the cloud side: the AS number of GCP is 16550.
- Address – Specify the peer IP address of the cloud side. Enter the IP address and subnet mask in dotted quad format and not CIDR notation. For example, specify
-
Click Update.
Step 4 - Create a CLI Add-On feature template
You also need an add-on CLI template.
To create a CLI Add-On feature template
-
Find a template for the C8000v device model and a type of CLI Template and copy it.
-
Enter a name for the template and a description and click Copy.
-
Edit the template (click the ellipsis … for the new template and choose Edit) and copy the following lines into the CLI Configuration section.
-
Click Update.
Step 5 - Update your device template
Next, we need to add the feature templates to the copy of the default device template and then define the values for the added features.
To add the feature templates to the device template
-
In the Device tab of vManage Templates, find the copy of the device template that you created in Step 1 and click the ellipsis (…) and choose Edit.
-
In the Service VPN tab, click +Add VPN.
-
In the Available VPN Templates, highlight the template created in Step 2, click the arrow to move it to the Selected VPN Templates, and click Next.
The select sub-templates step appears. - From the Additional Cisco VPN Templates, click Cisco BGP.
- From the Cisco BGP menu, choose the BGP template you created in Step 3 and click Add.
-
In the Additional Templates tab, select the CLI Add-On template you created in Step 4 and click Update.
A screen appears that lists the updated device template. You need to edit this template to add values for the new fields and associate an MVE. -
Click the ellipsis (…) and choose Edit.
The device settings appear with new fields defined in the feature templates.
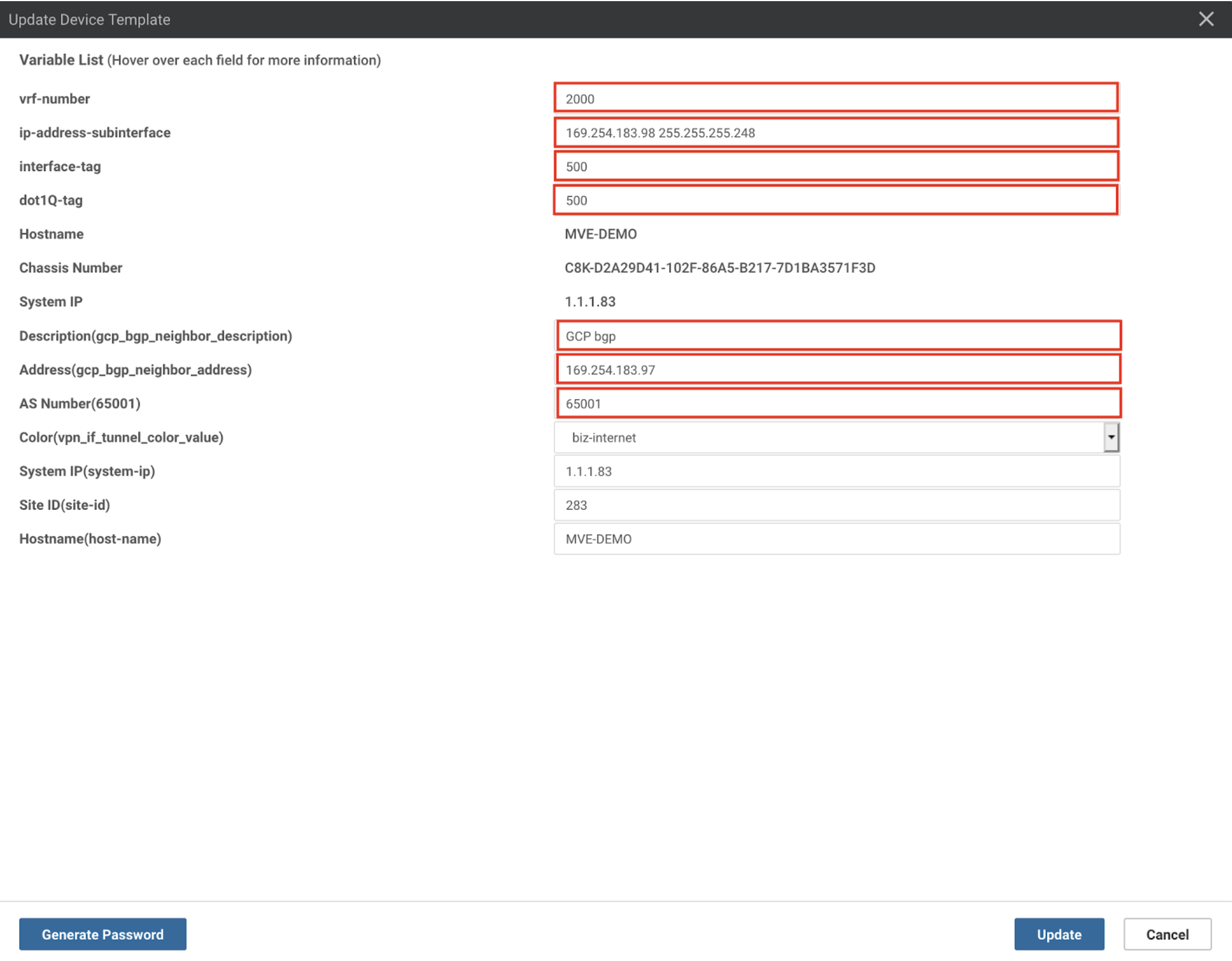
- Enter values for these new fields:
- vrf-number – Specify the VRF number (VPN ID) for the interface.
- ip-address-subinterface – Specify the IP address of the interface. This is the IP address assigned by GCP. You can confirm the IP address from the GCP console.
- Interface-tag – This value is the same as dot-1q-tag. You can find this value in the VXC connection details on the Megaport Portal: click the VXC name, choose Details, and use the A-End VLAN value.
- dot-1q-tag – This value is the same as interface-tag. You can find this value in the VXC connection details on the Megaport Portal: click the VXC name, choose Details, and use the A-End VLAN value.
- Description(gcp_bgp_neighbor_description) – Enter a meaningful description of the template for the BGP peer.
- Address(gcp_bgp_neighbor_address) – Specify the peer IP address of GCP cloud router. You can find the IP address in the GCP console.
- AS Number – Specify the AS number of the MVE.
-
Click Update.
vManage displays a preview of the configuration. Click Config Diff to review the changes. (Changes are highlighted in green.) -
Select the MVE in the device list.
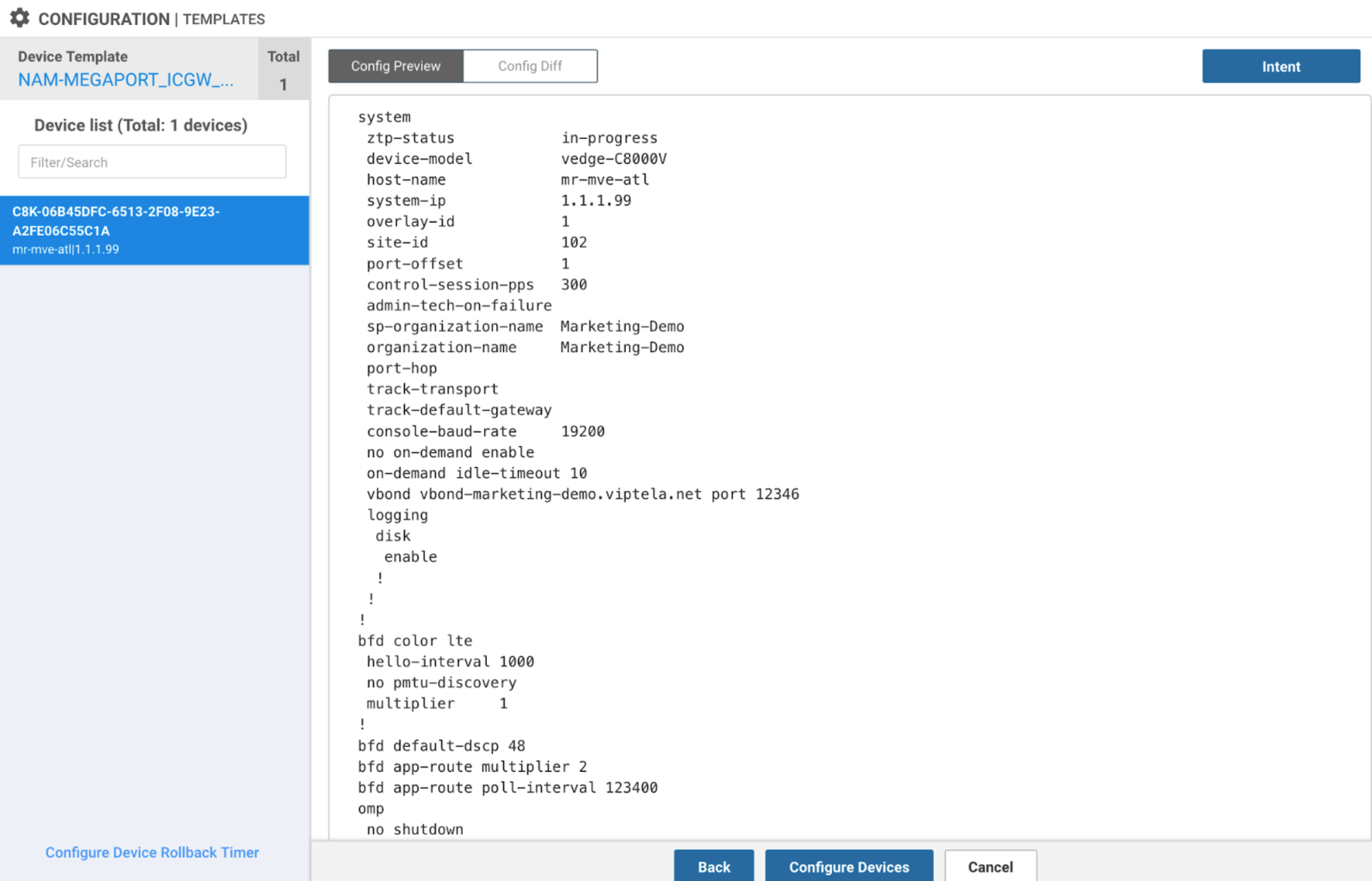
-
Review the changes and click Configure Devices.
vManage loads the template. When complete, the status indicates success.
The VLAN attachment and the BGP session will appear on the GCP console.