Creating MCR Connections to Azure using ExpressRoute
You can create a VXC from an MCR to Microsoft Azure ExpressRoute through the Megaport Portal. You can create the VXC to Azure from the MCR and establish either private or Microsoft peering.
To connect to ExpressRoute using MCR, you need an ExpressRoute service key obtained from the Azure Resource Manager (ARM) portal. Follow the steps in the Microsoft topic Tutorial: Create and modify an ExpressRoute circuit to get this key.
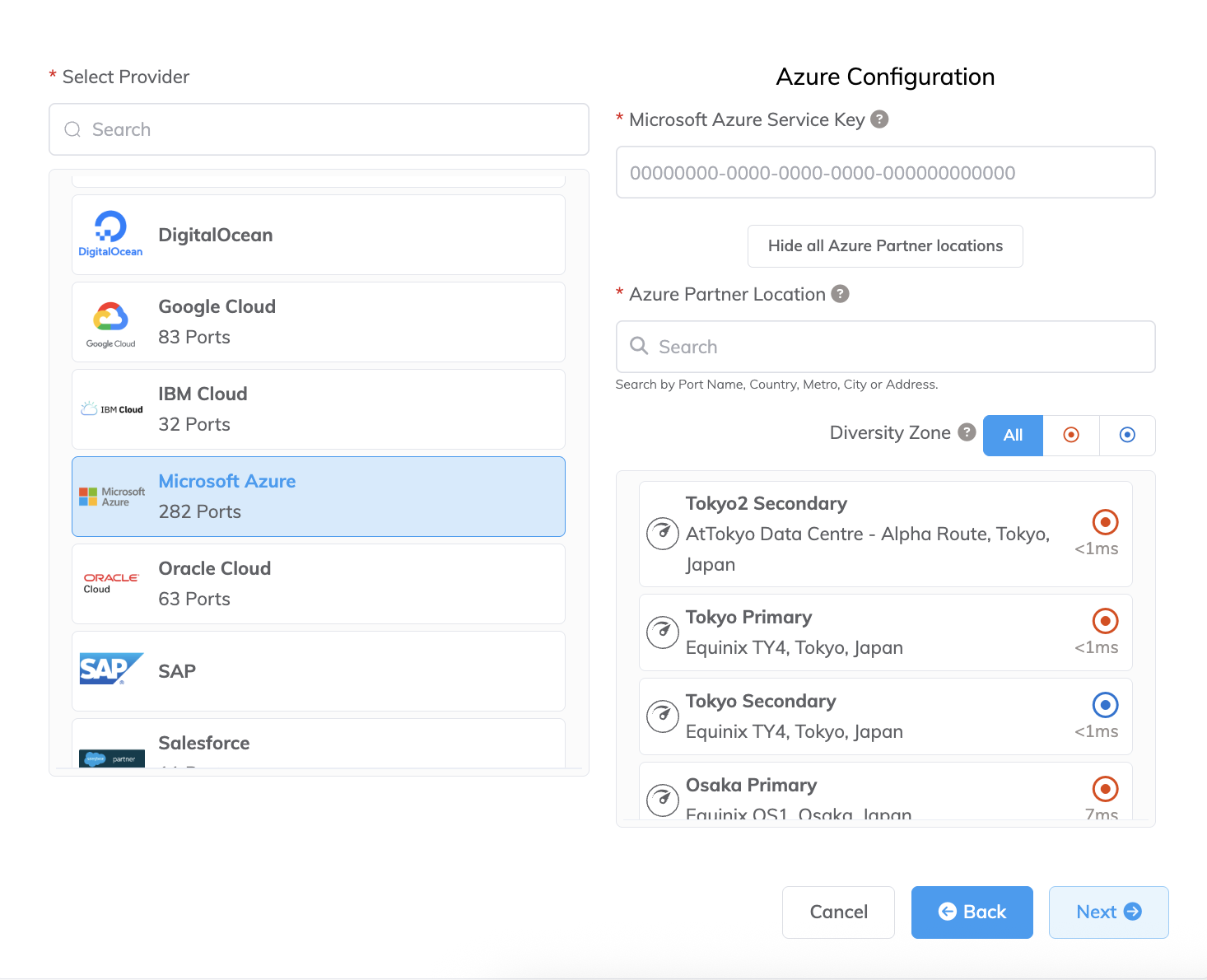
To check the latency and price of connecting to a particular Azure Partner location, start the procedure to add a connection to Microsoft Azure but instead of providing a Microsoft Azure Service Key, click View all Azure Partner locations. You can proceed to the Connection Details page without a service key and review the pricing of the selected port. To place an order for a Microsoft Azure connection, you need to provide a service key.
To create a VXC from an MCR to Azure
- In the Megaport Portal, go to the Services page and select the MCR you want to use.
-
Add a VXC connection for the MCR.
If this is the first connection for the MCR, click the Microsoft Azure tile. The tile is a shortcut to the configuration page. Alternatively, click +Connection, click Cloud, then click Microsoft Azure.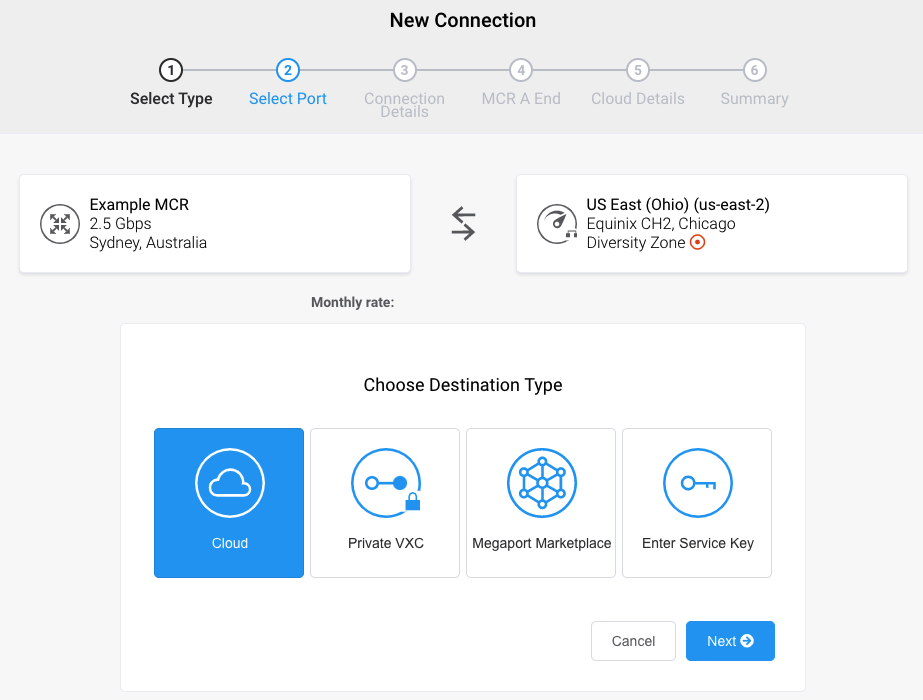
-
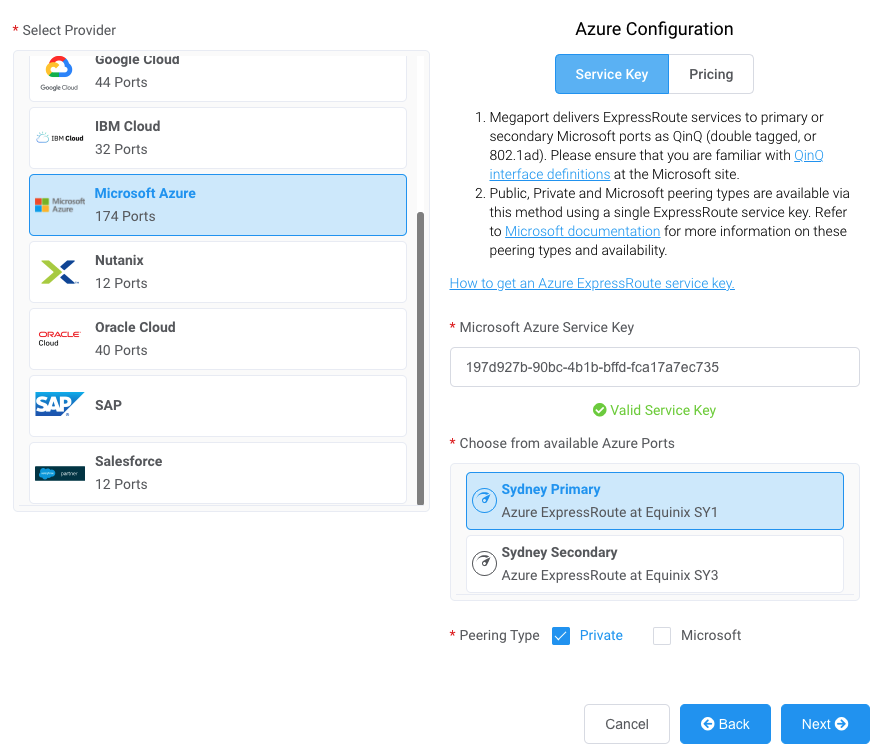
Add the ExpressRoute service key into the Microsoft Azure Service Key field.
The Portal verifies the key then displays the available port locations based on the ExpressRoute region. - Select the connection point for your first connection.
-
Select one or both of the peering types: Private and Microsoft.
-
Click Next.
-
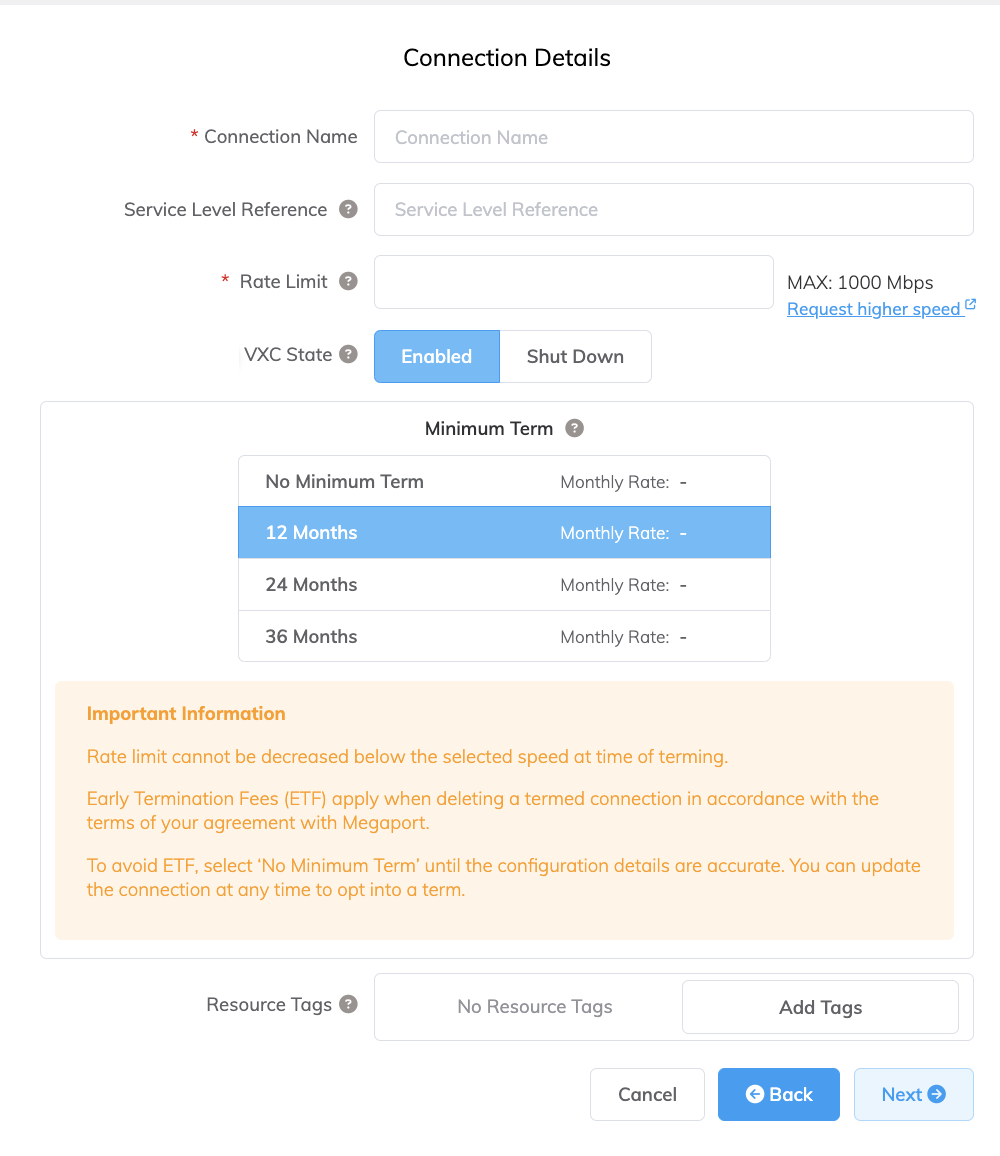
Specify the connection details:
-
Connection Name – The name of your VXC to be shown in the Megaport Portal.
-
Service Level Reference (optional) – Specify a unique identifying number for your Megaport service to be used for billing purposes, such as a cost center number, unique customer ID, or purchase order number. The service level reference number appears for each service under the Product section of the invoice. You can also edit this field for an existing service.
-
Rate Limit – The speed of your connection in Mbps. The rate limit for the VXC will be capped at the maximum allowable based on the ExpressRoute service key.
-
VXC State – Select Enabled or Shut Down to define the initial state of the connection. For more information, see Shutting Down a VXC for Failover Testing.
Note
If you select Shut Down, traffic will not flow through this service and it will behave as if it was down on the Megaport network. Billing for this service will remain active and you will still be charged for this connection.
-
Minimum Term – Select No Minimum Term, 12 Months, 24 Months, 36 Months, 48 Months, or 60 Months. Longer terms result in a lower monthly rate. 12 Months is selected by default. Take note of the information on the screen to avoid early termination fees (ETF).
Enable the Minimum Term Renewal option for services with a 12, 24, 36, 48 or 60-month term to automatically renew the contract at the same discounted price and term length at the end of the contract. If you don’t renew the contract, at the end of the term, the contract will automatically roll over to month-to-month contract for the following billing period, at the same price, without term discounts.
For more information, see VXC Pricing and Contract Terms and VXC, Megaport Internet, and IX Billing.
-
Resource Tags – You can use resource tags to add your own reference metadata to a Megaport service.
To add a tag:- Click Add Tags.
- Click Add New Tag.
- Enter details into the fields:
- Key – string maximum length 128. Valid values are a-z 0-9 _ : . / \ -
- Value – string maximum length 256. Valid values are a-z A-Z 0-9 _ : . @ / + \ - (space)
- Click Save.
If you already have resource tags for that service, you can manage them by clicking Manage Tags.
Warning
Never include sensitive information in a resource tag. Sensitive information includes commands that return existing tag definitions and information that will identify a person or company.
-
-
Continue with the default settings and click Next through the next screens to place the order, check out, and deploy.
The Megaport system takes about five minutes to deploy and configure the required peering types.
Viewing the configuration
Once the VXC connection deploys successfully, it is attached to the MCR on the Megaport Portal Services page:
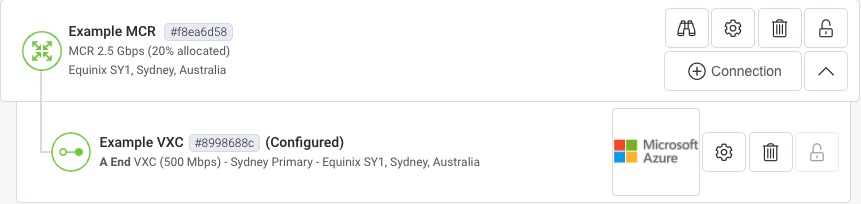
-
Click the VXC to display the details of this connection.
-
Select the Configure A End tab of the VXC detail to view this information:
- VLANs – 100 and 200 by default. 100 for Private peering and 200 for Microsoft.
- Local ASN – 133937. This is the default Megaport autonomous system number (ASN).
- Peer ASN – For Microsoft Azure via ExpressRoute, 12076 for all peering types.
- Local IP and Peer IP – Reflects the APIPA range for BGP peering (auto-configured) on Private peering. Microsoft peering displays a Megaport-assigned public IP range (within 117.18.80.0/21).
- BGP Password – Blank by default; this field is not mandatory for ExpressRoute connection because they traverse a private (non internet) path. However, if you enter a BGP password, you also need to update it manually on the ExpressRoute configuration page to match. The passwords do not synchronize automatically for security reasons.
Confirming ExpressRoute configuration details
The corresponding ExpressRoute details screen in the Azure portal shows that the Layer 2 connection is up (Provider Status = Provisioned) and Layer 3 for the Private (or Microsoft) peering is similarly configured:
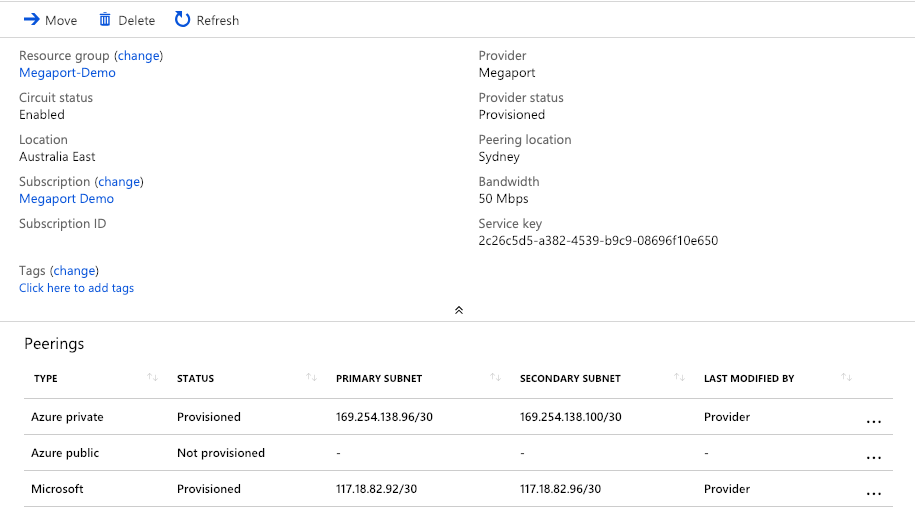
- Click the Azure private peering type to display the Private peering configuration.
Values for both primary and secondary subnets are provided, regardless of whether only one of these peering locations is established. If you add a second ExpressRoute VXC using this service key, it will inherit the same peering types and automatically configure for the next available IP address allocation within that peering type.
Creating and linking a Virtual Network Gateway
In addition to the ExpressRoute circuit, you need to create a Virtual Network Gateway (VNG) and associate it with both VNets used for private peering, as well as linking the VNG to your ExpressRoute circuit to provide routing on the Azure side toward the MCR.
Note
The creation of the VNG can take approximately 45 minutes, although this is a one-time requirement.
For more information, follow the steps in Configure a virtual network gateway for ExpressRoute using the Azure portal to create the VNG. Note that Microsoft charges apply per the ExpressRoute Gateways section of the Azure VPN gateway pricing page.
After you create the VNG, you need to associate the ExpressRoute VNG to the ExpressRoute circuit by following Connect a virtual network to an ExpressRoute circuit using the portal guidance.
Using a service key
You can create a service key that allows you to share your service with another Megaport account holder. For more information, see Setting up Service Keys.
Troubleshooting
How do I confirm the BGP configuration?
To confirm a successful BGP/Layer 3 configuration, return to Azure private peering, click the detail line and then click Get ARP Records.
This function takes about a minute to populate data. For a successful connection you see a display similar to this image, indicating that the MAC addresses have resolved on both the On-Prem and Microsoft sides of the connection:
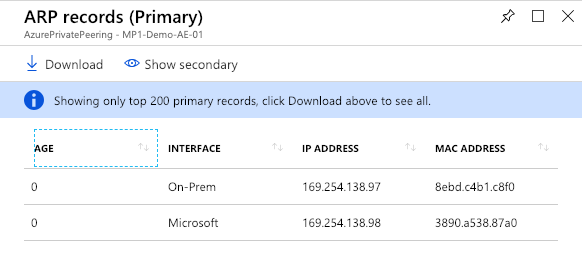
After switching from primary to secondary, this display currently only shows a value for the Microsoft side of the connection, because the VXC to the secondary target has not been configured.
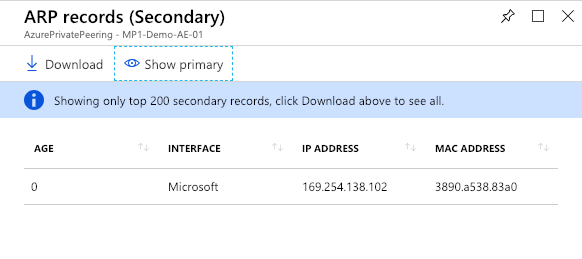
To configure the secondary VXC, create another VXC from your MCR with the same ExpressRoute service key; however, this time target the secondary router presentation.
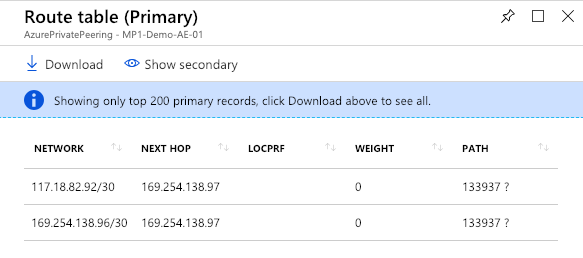
Once Layer 3 BGP is active and confirmed, you can view the Route Table as seen by the Microsoft edge devices by clicking Get route table in the Private peering pane. It displays the next hop, weighting, and AS path for the network values. You can toggle the display to view the secondary path route table when both primary and secondary VXCs are active.
My public prefix configuration is the “verifying” state. What can I do?
When you create a public circuit and you specify public peer IP addresses, you need approval from the Microsoft Azure team (private circuits do not require this authorization and are available within minutes). Before approving public peer IP prefixes or public ASNs, the Azure team needs to verify the ownership by confirming that the advertised public prefixes and peer ASN are assigned to the organization listed in your Azure account. If you are getting the public prefixes from another entity, and the assignment is not recorded with the Internet Routing Registry, the validation will not complete.
Resolution
If the public virtual interface state is in the verifying or validation needed state for more than 72 hours, check the email address registered to your Azure account. You might have received an email from the Azure team if the owner of the BGP ASN or one of your advertised routes does not match your account details.
If the BGP ASN or an advertised route does not match your account, collect the documents that show the public prefixes are assigned to your organization by the entity that is listed as the prefix owner in the routing registry. Submit these documents for manual validation by opening a support ticket for the Azure team.