Planning Your Fortinet FortiGate Deployment
This topic provides an overview of the provisioning process and describes deployment considerations for the Megaport Virtual Edge (MVE).
| You Provide | Megaport Provides |
|---|---|
| Internet connection from branch | Platform to host virtualized network function (VNF) appliances |
| VNF vendor enabled at branch | Complete connection from a branch to any destination on the Megaport network and interoperation with other Megaport products and services |
| Customer premises equipment (CPE) installed in branch | Megaport Internet connection to terminate the tunnel between MVE and CPE at branch via internet |
| VNF software license to use on Megaport SDN | Access to the Megaport ecosystem |
Fortinet FortiGate features
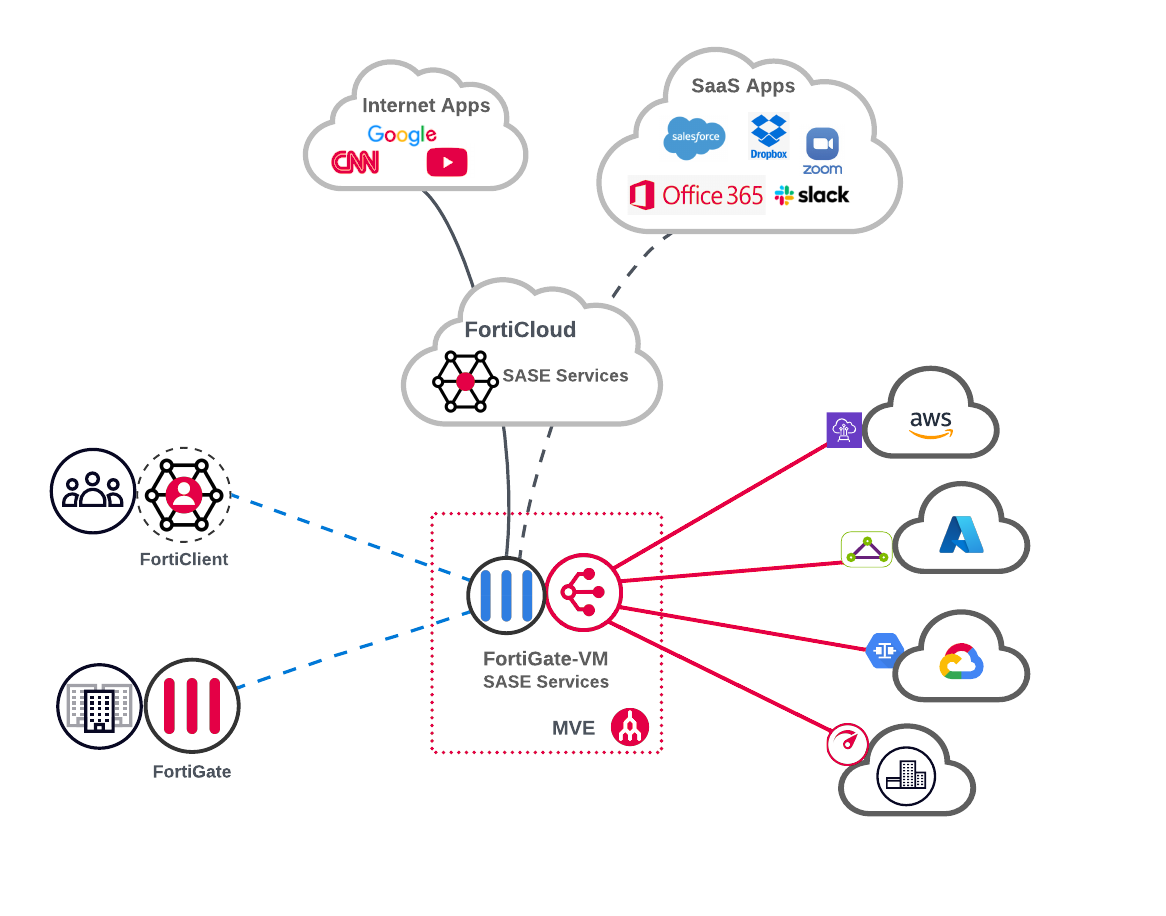
The FortiGate-VM delivers both NGFW and SD-WAN services on a single virtual machine. Hosting the FortiGate-VM on MVE not only optimizes edge-to-cloud network connectivity, but also enforces advanced security services and policies across the Megaport backbone segments.
Embedding the FortiGate-VM into Megaport’s NaaS platform extends the following core Secure Access Service Edge (SASE)Secure Access Service Edge (SASE) is a security framework combining security and network connectivity technologies into a single cloud-delivered platform to enable secure and fast cloud transformation.
elements between the edge and cloud network fabric:
-
Next-generation firewall (NGFW), including stateful firewall policies, network address translation (NAT), intrusion protection services, Secure Sockets Layer (SSL) inspection, and threat intelligence.
-
Secure web gateway (SWG) services protect devices from malicious internet destinations using web content filtering and malware scanning.
-
Zero trust network access (ZTNA), which controls access to applications by verifying users and devices before every application session and confirms that they meet the organization’s policy to access that application.
The FortiGate-VM also supports remote user integration with Fortinet SASE solutions using their FortiClient endpoint security agent. The FortiClient enables the device to connect securely to the security fabric over either VPN (SSL or IPsec) or ZTNA tunnels.
The FortiSASE solution allows both the FortiGate and FortiCloud services to be used in a blended design as well. For example, internet and select SaaSSoftware as a Service (SaaS) is a form of cloud computing in which the provider offers the use of application software to a client and manages all the physical and software resources used by the application. SaaS is sometimes referred to as “on-demand software” and is usually priced on a pay-per-use basis or using a subscription fee.
applications might be protected using both SWG and a cloud access security broker (CASB) through FortiCloud, while private Megaport connections are protected using FortiGate security services.
Note
If you have already deployed a Fortinet firewall, you can connect it to an MVE so that your headquarters or branches can access cloud services over private interconnects.
For more information about these features, see:
Deployment considerations
This section provides an overview of the MVE deployment options and features.
Fortinet FortiGate uses virtual FortiGate appliances or physical FortiGate appliances much like many other VNF vendors. However, with Fortinet, you can configure the appliances for several different uses. For example, you can configure a Fortinet appliance for use:
-
Strictly as a next-generation firewall (NGFW) for remote offices with local configuration and local logging only.
-
As central management with central logging, or as central management without central logging.
-
In a traditional SD-WAN style overlay network.
For more information, see the Fortinet Documentation Library.
VNF appliance vendors integrated with MVE
MVE is integrated with Fortinet FortiGate, which uses the Fortinet FortiManager console to create the private overlay network.
For information about all supported NFVsThe MVE is an on-demand, vendor-neutral Network Function Virtualization (NFV) platform that provides virtual infrastructure for network services at the edge of Megaport’s global software-defined network (SDN). Network technologies such as SD-WAN and NGFW are hosted directly on Megaport’s global network via Megaport Virtual Edge.
on the MVE platform, see the Megaport Virtual Edge (MVE) product page.
MVE locations
For a list of global locations where you can connect to an MVE, see Megaport Virtual Edge Locations.
Sizing your MVE instance
The instance size determines the MVE capabilities, such as how many concurrent connections it can support. To size your MVE correctly, consult the vendor’s sizing documentation to ensure it aligns with the number and type of features you plan to enable.
When choosing an MVE instance size, keep in mind these items:
-
Any increase on the network data stream load can degrade performance. For example, establishing secure tunnels with IPsec, adding traffic path steering, or using deep packet inspection (DPI) can affect the maximum throughput speed.
-
Future plans to scale the network.
To check which MVE instance sizes are available for your deployment, use the Megaport Portal during the MVE setup process. Instance size availability depends on both the selected vendor and the deployment location, and might vary accordingly. The Megaport Portal displays the sizes that are available for your selected vendor and location.
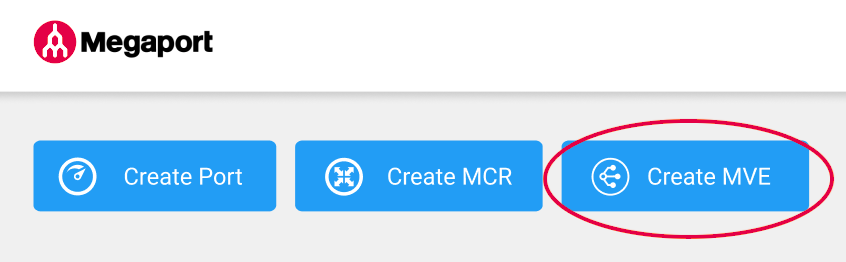
To check the MVE instance sizes in the Megaport Portal
- In the Megaport Portal, go to the Services page.
-
Click Create MVE.
-
Select Fortinet FortiGate-VM.
-
Select the software version.
-
Click Next.
-
Select an MVE location.
Select a location geographically close to your target branch and/or on-premises locations.
You can use the Search field to find the Port name, Country, Metro City, or address of your destination Port. You can also filter by diversity zone.
-
A list of available instance sizes appear based on the selected location. Available sizes are highlighted in green and labeled Available. The sizes support varying numbers of concurrent connections, and individual partner product metrics vary slightly.
Note
If the MVE size you want is not in the list, then there is not enough capacity at the selected location. You can either select another location with enough capacity or contact your Account Manager to discuss requirements.
What if I need more MVE capacity in the future?
To increase your MVE capacity, you have these options:
-
You can provision another MVE instance, add it to your overlay network, and split the workload between the two MVEs.
-
You can provision a larger MVE instance, add it to your overlay network, migrate connections from the old MVE to the new larger MVE, and then retire the old MVE.
You can adjust the Megaport Internet bandwidth at any time without having to tear down the virtual machine.
Security
MVE provides secure capacity to and from your internet-enabled branch locations, to any endpoint or service provider on the Megaport SDN. CSP-hosted instances of partner SD-WAN products route critical traffic across the Megaport SDN, reducing internet dependence. Traffic remains encrypted and under your policy control while traveling across the Megaport SDN, to or from, MVE.
Fortinet FortiGate includes access to a comprehensive security feature: Secure Access Service Edge (SASE)Secure Access Service Edge (SASE) is a security framework combining security and network connectivity technologies into a single cloud-delivered platform to enable secure and fast cloud transformation.
. Fortinet on MVE natively supports SASE and SD-WAN services. For more information, see SSE and SASE within the Megaport Network.
Licensing
You bring your own Fortinet (FortiGate) SD-WAN license for use with MVE. It is your responsibility to have the appropriate licenses for the SD-WAN endpoints created on the Megaport network.
VLAN tagging
Megaport uses Q-in-Q802.1Q tunneling (also known as Q-in-Q or 802.1ad) is a technique used by OSI Layer 2 providers for customers. 802.1ad provides for both an inner and an outer tag whereby the outer (sometimes called S-tag for service provider) can be removed to expose the inner (C-tag or customer) tags that segment the data.
to differentiate VXCs and MVEs on a host hardware system. The tenant MVE receives untagged traffic for the internet-facing link, and single-tagged 802.1Q traffic for VXCs toward other destinations on the Megaport network (such as CSP on-ramps or other MVEs). For more information, see Configuring Q-in-Q.
vNICs
Each MVE can have up to five vNICs. An MVE is created with one vNIC by default. You can add up to four more, making a total of five.
Before specifying the number of vNICs on your MVE:
-
Be aware that the number of vNICs cannot be changed after an MVE has been ordered. Decide in advance how many vNICs to specify when you create the MVE.
-
Consult your service provider to make sure that functionality won’t be affected if you add a vNIC.
Note
If you need to change the number of vNICs after an MVE has been ordered, you will have to cancel and re-order the MVE.
For more information, see Types of vNIC Connections.